Two major American newspapers have printed contrasting views about the issue of Edward Snowden and whether he deserves clemency or a pardon. Many are familiar with the New York Times' take, as it was received with some fanfare here. Their argument was basically that Snowden revealed a treasure trove of information and therefore deserved "some form of clemency." The LA Times issued a quasi-rebuttal on January 7, noting, for example,
"And it’s hyperbole to argue, as The New York Times does in its editorial, that Snowden’s revelations prove that 'government officials have routinely and deliberately broken the law.'”
The LA Times understood that the Snowden treasure trove almost exclusively involved information that had nothing to do with Americans or the Constitution. In the remaining paragraphs, I intend to carefully establish why they're both wrong.
I. THE NEW "SHOTGUN-STYLE" TOP SECRET INFORMATION DISCLOSERS
The first argument against a Presidential Pardon or Executive Clemency for Snowden boils down to two words: Negative Reinforcement.
Behavioral psychologists know that reinforcement can affect behavior. Our tax code is mostly negative and positive financial reinforcement, at least when it comes to deductions, promoting some behaviors while discouraging others. Does Government want to promote or discourage the behavior of individuals like Edward Snowden and Chelsea Manning?
a. A Shotgun of Information Sprayed Willy-Nilly into the Information Marketplace
What happened with the Manning information was a document dump that was akin to taking a loaded data shotgun and firing it 750,000 times into the information marketplace not knowing if you might hurt someone. Snowden has taken a few more precautions, but as you'll see below in the subheading entitled "Damage to American Intelligence-Gathering Capabilities," there has still been a deleterious effect.
Should a person be allowed to steal thousands or tens of thousands, even hundreds of thousands of Top Secret documents, disperse them into the wind, and then be allowed to point to one of the documents and say, "There. See. I was justified"? Should that behavior be encouraged or discouraged? Is such a blunt, dangerous and ugly process even necessary? And who gets to decide that " X " is a violation of the Constitution significant enough to permit the disclosure of 100,000 or 200,000 secrets?
In the case of sensitive military and intelligence-gathering information, I think the answer is obviously that a Government must discourage that kind of behavior, especially when there are alternative remedies available.
b. There Are Established and Effective Whistleblowing Procedures in Place
One question thrown about a lot in this debate is "Who elected Snowden?" That question deals with two fundamental issues: (1) Who decides, and (2) How should they decide. In a Democracy, officials are elected who appoint judges to determine questions of constitutionality. They also appoint officials to determine what should and shouldn't be classified and kept from the public at large. Legislators have also provided a system in which whistleblowers can bring attention to issues involving governmental illegality or waste.
That whistleblower system was effective enough in 2012 to encourage more than 1,000 people to contact the Office of Special Counsel. In fact, six months before anyone had heard of Edward Snowden, the OSC reported:
OSC is meeting its duties as an independent investigative and enforcement agency, bringing greater integrity and efficiency to the federal government. OSC is working harder, smarter and with better results than at any time in its history. The agency resolved 1,037 more cases in FY 2012 than in FY 2009. That is a 31% increase, even though staffing levels have remained largely unchanged these four years. Total favorable actions in PPPs in 2012 have increased by 89% over 2011 levels. The USERRA DP for veterans has achieved a 26% favorable resolution rate. More whistleblower disclosures have been resolved, 1,053, than in any previous year. This has truly been a record-setting year.
(emphasis added; Page 10 of the linked pdf). Thousands more contacted the Securities and Exchange Commission. Also well before Snowden, President Obama received praise from the Government Accountability Project for fighting for and ultimately enacting the Whistleblower Protection Enhancement Act of 2012, which included among its reforms provisions that would have applied to Snowden had he elected to follow that route, including:
"... federal employees now are protected (in addition to already-existing scenarios) from reprisal if they: are not the first person to disclose misconduct; disclose misconduct to coworkers or supervisors; disclose the consequences of a policy decision; or blow the whistle while carrying out their job duties."
Specifically, there was a mechanism in place since 2008 for Snowden to blow the whistle in a way that did not harm the country and still got the job done. This was the specific regulation in effect at the time he left for Hong Kong (highlighted in pink):
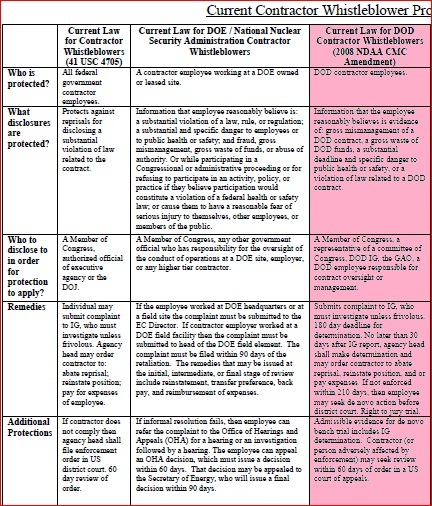
Additionally, there has been whistleblower protection for DOD contractor employees since at least 2006 found in the Code of Federal Regulations. Title 48 of the Code of Federal Regulations, Subpart 3.9 reads as follows:
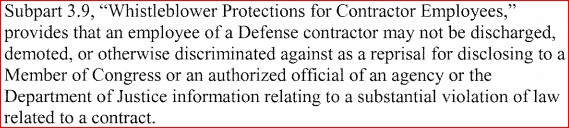
Statement of Acting DOD Inspector General Gimble, Feb. 14, 2006, at p. 5.
II. DAMAGE TO AMERICAN INTELLIGENCE-GATHERING CAPABILITIES
a. Der Spiegel/Applebaum/"The Catalog"
The documentation that Snowden stole was disseminated to a number of people, and at least one of those individuals, Jacob Applebaum, working with Der Spiegel, has provided veritable seminars of information which could prove useful to terrorists, enemy states and high-end drug cartels. For example, here's a screengrab showing Applebaum during his "seminar," with a picture of one of the top secret NSA devices projected on a screen, including its specifications, and this device can be loaded into a drone to obtain wireless information from an unfriendly target while flying eight miles away:

APPLEBAUM @ 16:13 of video linked above: "Here's an example. First Top Secret document of the talk so far. This is a close access operations box.... They say the attack is undetectable.... They say they can do this from as far away as eight miles to inject packets. So, presumably, using this they will be able to exploit a kernel, some vulnerability of some kind, parsing the wireless frames, and I've actually heard ... that they put this hardware in drones."
If you are the head of security for a terrorist organization or a drug cartel, what do you do with this information? I would bet that you set up drone observation posts, if not already in place, and institute a protocol of radio silence as soon as a drone is spotted. Below is another of the many top secrets that Applebaum gave away, this one detailing a hardware implant that the NSA could purportedly put into a computer sold to a foreign intelligence target. What is pictured below is a screengrab of exactly where inside the computer you might find the device:

APPLEBAUM @ 53:03 of video linked above: "Here's a USB hardware implant.... It will provide a wireless bridge into the target network with the ability to load exploits.... And here's where you look for it."
Again, if you are the head of security for a terrorist organization, enemy state or a drug cartel, what do you do with this information? I would bet that you'd open up all of your computers to look for this device. Most importantly, you would hold a seminar for all of your employees to go over everything exposed in the Applebaum talk or contained in the pages of Der Spiegel.
b. Other Valuable Bytes of Information for Terrorists and Foreign Governments
In the LA Times Editorial from January 7, the editors noted the following about a few of the other bytes of information that harm America's intelligence-gathering capabilities:
"Snowden also gave the Guardian a document showing that the NSA had intercepted the communications of then-Russian President Dmitry Medvedev during a Group of 20 summit in London in 2009. And Snowden revealed in an interview the specific dates and the IP addresses of computers in Hong Kong and on the Chinese mainland that had been hacked by the NSA over four years. Disclosing intelligence operations directed at foreign countries does nothing to protect Americans' privacy, and it doesn't seem to us like whistle-blowing.”
(quoting
The New York Times editorial).
Most recently, Snowden material has been published that has outted an NSA agent and given a violent terrorist organization the heads-up on exactly how they are being spied on.
III. WHAT SNOWDEN ULTIMATELY REVEALED WAS THAT SPIES SPY, THAT GOVERNMENTS SPY ON GOVERNMENTS, AND THAT THERE IS A STRENUOUS THREE-BRANCH OVERSIGHT PROCESS INVOLVING NSA PROGRAMS
a. Worst-Case Scenario.
At the very worst, there has been an active NSA program culling metadata that is so not-bad that even the panel that said it was illegal called for a "winding down" period. The one Judge who has ruled the program to likely be unconstitutional also stayed his injunction. Think about it this way: Would a federal judge have asked Al Capone to "wind down" his activities? Would a police officer, having caught someone driving 60 in a 15 mph school zone, stayed any enforcement against that driver?
One of the reasons that the program is so not-bad and has been held constitutional by sixteen different judges on thirty-six separate occasions is because it is based on thirty-four-year-old United States Supreme Court precedent. Since the decision in Smith v. Maryland, 442 U.S. 735 (1979), it has been settled law that obtaining telephone metadata does not constitute a search under the Fourth Amendment. The rationale given by the Supreme Court was that a person did not have a "reasonable expectation of privacy" with regard to that information because the person was freely handing it over to a third party--the telephone carrier. Not stated in the opinion is the fact that telephone metadata (i.e. a telephone number, the number called, the duration of the call, and the time of the call) is not really a search because even if you have that information, with nothing more, you've got this:
Does that really constitute a search? That may be the worst search ever. To illustrate the point, think of a game of "Hide and Seek" in which you have to find me, knowing only that (a) I am a person, (b) I am somewhere in the United States, and (c) I have an internet connection of some sort. Worst. Search. Ever.
b. < 300 Unique Queries.
What we've found out is that during the entire year of 2012, the NSA ran a grand total of less than 300 queries of the data. Here's a screengrab of a letter sent by the Department of Justice and maintained on the ACLU website establishing that fact:
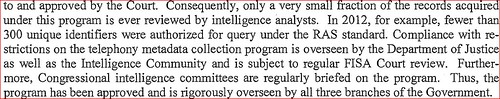
The procedures call for one of the twenty approved NSA agents to run queries only for telephone numbers that have been directly linked to terror actors or their foreign facilitators and financiers. For example, if other on-the-ground intelligence had identified a telephone number belonging to terror suspect
Ayman Al-Zawahiri or one of his lieutenants, the NSA would "query" that phone number in the database to see if Al-Zawahiri had called any numbers in the United States. That type of search occurred less than once per day in 2012.
c. Actually There Are Four "Branches" of Government Providing Oversight.
We learned recently that there is a Privacy Panel created specifically to provide oversight for matters like this. The Privacy and Civil Liberties Oversight Board was created by act of Congress in 2004, but President Bush failed to get it up and running. President Obama forced it into action in 2011, with nominations of the five board members, having to re-nominate three of them because Republicans initially refused to confirm them. It is independent of the judiciary, the executive and the legislature. So, back in December 2011, about a year and a half before anyone had ever heard about Edward Snowden, the Administration went on the record as follows:
Independently established by Congress, the Board’s function is to analyze and review the actions of the executive branch and ensure that concerns with respect to privacy and civil liberties are appropriately considered in the implementation of laws, regulations, and executive branch policies related to counter-terrorism.
In the end, 98.5% of Snowden's revelations have had nothing to do with the Constitution or the privacy rights of Americans; rather, they deal with foreign spycraft. In my opinion--and I think it is patently obvious--Snowden's revelations about foreign spycraft will harm the country. Moreover, because of the public relations response to the issue, we've seen that there is a stringent, multi-tiered oversight mechanism scrutinizing that one domestic NSA program, including the following:
1. Judicial
a. Including hands-on forward reaching rulings that determine if a newly requested search is legal.
b. Periodic "wellness checks" of the system by the FISA Courts to make sure that what the NSA has been doing is still constitutional.
c. Right to appeal
2. Legislative
a. Hearings in the House
b. Hearings in the Senate
c. Laws enacted by Congress
3. Executive
a. Regulations drafted by the Executive Branch (most notably the DOJ)
b. Intra-agency regulations
c. Intra-agency supervision
d. Civil Liberties Protection Officers
e. Inspectors General
4. Independent
a. Privacy and Civil Liberties Oversight Board
b. The Whistleblower System, which could go through the Judiciary or Executive or the Legislative branch.
c. The right of the carrier to be heard.
d. The media
IV. BELIEF IN GOVERNMENT AND IN THE RULE OF LAW
Suspicion of Government and Government employees has become
the defining characteristic of Fox News. Democrats, on the other hand, have always been much more on the side of Government employees, although reasonably leery of the upper-echelon military. Most Democrats realize that NSA workers are trying to strike a balance between privacy and security, with the latter being an essential feature of all governments and the former being a linchpin in our unique system. Should we expect an entire agency to act perfectly at all times? Of course not, that's ridiculous. Should we expect an entire agency to turn its back on Executive, Judicial and Legislative oversight, regulations, laws, on-site supervision, the potential for whistleblowing, possible prison sentences and the loss of employment? Again, no, that's ridiculous. Keeping everything in check is the rule of law. The rule of law ensures that "capability" never becomes "actual reality."
This leads to the "capability" versus "actual reality" dilemma. Sure, the United States Government has the capability to spy on every single person in the country. That capability has been with us for quite some time in one form or another, and it will be with us until the end of the republic. Our Government also has the capability, through its military, of destroying all domestic opposition and taking over the country. The Government could unleash the most spectacular biological agents and nuclear attacks ever known to mankind. But, that's the difference between capability and actual reality.
For individuals interested in a healthy democracy, a functioning and viable whistleblower system is essential. Edward Snowden and his agents have played a public relations game to scare people about their Government, to make them suspicious of the whistleblower system, and to forget the rule of law. And that may be his greatest crime. For all of these reasons, Edward Snowden stands no chance of obtaining clemency or a pardon, and for the same reasons, The New York Times was wrong and lost in some strange hyperboleland, and the Los Angeles Times failed to go far enough in the other direction.


